As of July 29, 2014, the Cisco VPN Client will no longer be available to purchase or download and will no longer be supported. Make the most of your initial Cisco VPN gateway investment, and take remote access to the next level.
Provide your users with a reliable and simple—yet secure—VPN client that always works:
If you answered YES to at least one of these questions, there's no better time to take a closer look at the NCP centrally managed VPN Client Suite. Built from the ground up to be easy to use, the NCP Secure Enterprise Solution provides state-of-the-art VPN connectivity to Cisco gateways, and a robust environment for centrally managing clients.
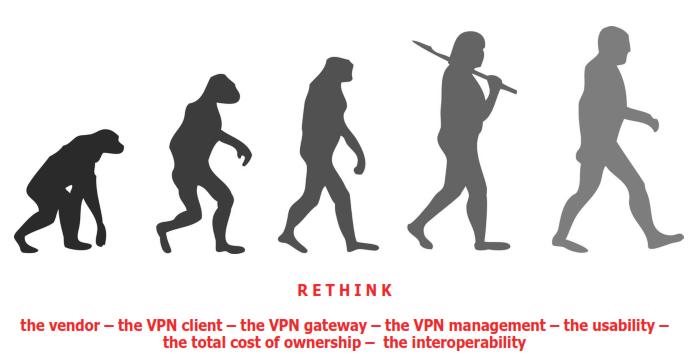
Rethink Remote Access:
Since 1986, the NCP engineering development team has continuously pushed to rethink how to allow enterprises to overcome the complexities of creating, managing and maintaining remote network access. Today's remote access technology translates to a patchwork of point solutions — mixed hardware and software — creating security loopholes, management headaches and frustrated end-users.
The worldwide leading "Next Generation Network Access Technology" by NCP solves these problems! The holistic remote access solution integrates all essential technologies regarding security and communication.
- Integrated IPsec/SSL VPN as one system
- Practical NAC function (Network Access Control)
- Management of 100,000+ remote users from one terminal (single point of administration)
- Central software updates and management
- Seamless access-point roaming
- Certificate creation, management with a few mouse clicks
- Perfect for Cloud Computing
- Reduce Costs for training, helpdesk and documentation
|
- Keeping the hardware you own
- Support for all end-device platforms
- One-click network access for users
- Secure on-the-fly policy changes
- Endpoint security without user interference
- Scale as needed without adding boxes
- Centrally-managed end-device firewalls
- Virtualization
- Communication in every Remote Access environment
|
Rethink The VPN Client:
NCP invests in client development, constantly improving performance, strengthening security and creating a true one-click, remote access experience. The user is the focus of any remote access system — unfortunately, enddevice client software is all too often viewed as a commodity. NCP engineering sees the user as the center of any system.
 The highlights in brief:
The highlights in brief:
- Connects to any IPsec compatible gateway
- Works on any Windows- or Linux-based OS (32/64), Apple OS X and Android OS
- One-Click-Solution
- Contains an integrated dynamic Personal Firewall
- Offers a built-in Internet Connector and Wi-Fi Registration
- Includes a wireless Budget Manager
- Includes SMS based two-factor authentication and supports different third party two-factor authentication systems
- Provides Multi-Certificate Support
- Prevents Users tampering with a settings lock
An Integral Part of the NCP Remote Access Solution
When implemented as the enforcement end of the holistic NCP remote access solution, administrators have unprecedented control over end-users, without compromising ease-of-use for remote staff.
NCP VPN Client Suite – universal, efficient and secure:
- Centrally-controlled NAC functions
- Automatic software updates
- Seamless Certificate Creation and Management
- Simple user provisioning and management
- Comprehensive firewall configuration
- Automatic VPN Path Finder™ Technology
Rethink the VPN Gateway:
NCP's gateway provides simple scaling and the ability to overlay existing hardware. The remote access gateway is often restricted to box form — hardware — requiring complex upgrades, expensive replacements and resourceintensive scaling. NCP engineering solves these problems.
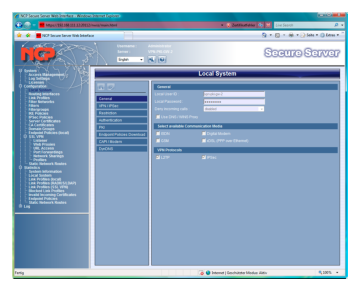 The highlights in brief:
The highlights in brief:
- Hybrid support of IPsec and SSL VPN
- Integrates with any Third-Party IPsec Gateway
- VPN tunneling with all major operation systems
- Handles 10,000+ concurrent connections
- Integrates IP Routing and Port Forwarding
- Provides Web Proxy and Portable LAN
- Offers Central or Distributed Installation
- Integrates Firewall Protections
- Easy Virtualization
- Certificate-based authentication of iOS end devices
Facilitator of Policy Enforcement for the NCP Remote Access Solution
When implemented as part of the holistic NCP remote access solution, policy changes can be made on-the-fly, while maintaining unprecedented control over end-users, without compromising network integrity.
NCP VPN Gateway – universal, efficient and secure:
- Enables NAC function enforcement
- Creates VPN Path Finder™ Technology
- Enforces certificate authentication
- Enforces multiple policies across any networks
Rethink the VPN Management:
emote access technology too often translates into a jumble of solutions, functionality compromises and policy limitations, requiring many administrators. NCP engineering solves these problems.
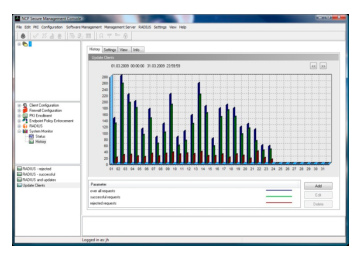 The highlights in brief:
The highlights in brief:
- One Administrator to handle 100,000+ remote users
- Client provisioning and configuration
- Client firewall configuration
- Remote access gateway configuration
- Practical NAC function management
- Certificate enrollment and management
- Software update push management
- Entire remote access monitoring and reporting
- Easy virtualization and multi-tenancy
- Perfect for Cloud Computing
- Built-In RADIUS server
- Cost-effective scaling and redundancy protection
- Comprehensive control over third-party software and hardware
- Microsoft Active Directory integration
The Center of the NCP Remote Access Solution
When implemented as the control hub of the holistic NCP remote access solution, companies can rethink their remote access entirely, while maintaining unprecedented control over end-users without compromising ease-ofadministration.
NCP VPN Management – universal, efficient and secure:
- Launch hosted "managed VPN" services
- Extend virtualization efforts
- Securely change policies on-the-fly
- Eliminate vendor lock entirely
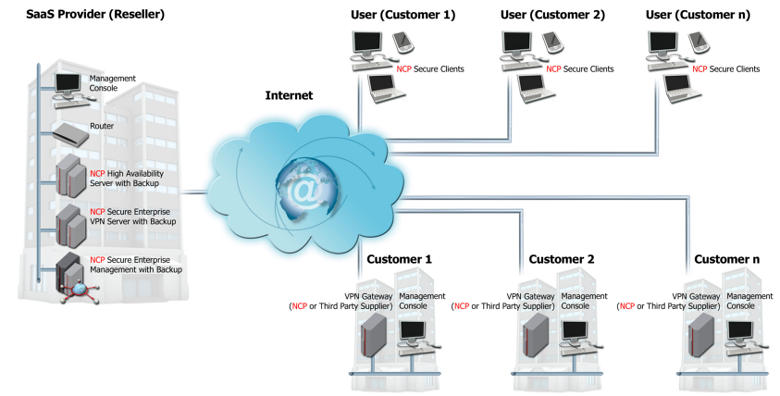
Rethink Remote Access: VPN "Out of the Cloud":
Secure remote access to the company network from within the Cloud
"VPN as a Service"
Requirements:
Full or partial outsourcing of VPN operation and management to a Cloud service provider.
Solution:
A provider has the option to:
- use existing resources within the cloud or
- to set up a VPN infrastructure of its own for its customers
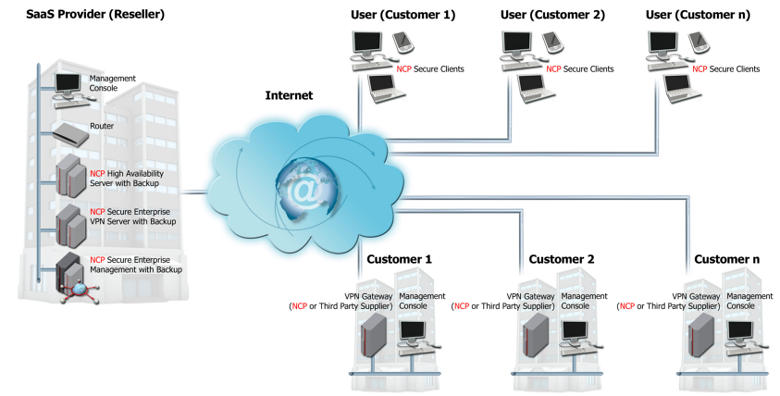
The customers' benefits:
- No investment in hardware, software and in-house experts
- Monthly bills instead of one-time investment with annual write-off
- Reduction of staff resources
- Top-notch security and communication at all times
- Fast implementation
- Well-designed technology
- "Easy VPN"
|
The SaaS providers' benefits:
- New source of income
- Good value for money
- Opening up of new customer groups
- Long-term customer connectivity
- Software-based, virtualized VPN solution
- Client ability
- High scalability
- Single point of administration
- Low operating costs
- Low personnel expenditure
- Client parameter locks
- Integrated centrally manageable Personal Firewall
- Central management of all clients via a single console
- Fully automatic operation
|
Rethink the Vendor:
Today's large network security vendors — hardware and software — focus on locking the market into proprietary solutions, to force return customers and drive the highest margin technology into the market, regardless of user requirements. NCP engineering acts different.
Stability Is Important
- 27 Years Remote Access Expertise
- Privately-Owned and profitable
- Established in North America
- Proven Partner Network
- OEM History with Deutsche Telekom,Cisco, Astaro and others
- 10,000+ Customers Globally
Innovation Is Important
- First to support 64-Bit Devices
- First to support Windows 7 and 8.1
- First to offer Secure Friendly Net Detection
- First to offer Dynamic VPN Path Finder™
- First to offer One-Click Client Suite
- First to solve VPN Management Complexity
Industry Expertise Is Important
- Serving Financial Services
- Serving Insurance Providers
- Serving the Manufacturing Industry
- Serving the Retail Sector
- Serving Government Organizations
- Serving Healthcare Providers
- Serving Educational Institutions
- Securing OEM Partners
You can trust this unique Remote Access Technology from NCP!
 As of July 29, 2014, the Cisco VPN Client will no longer be available to purchase or download and will no longer be supported. Make the most of your initial Cisco VPN gateway investment, and take remote access to the next level.
As of July 29, 2014, the Cisco VPN Client will no longer be available to purchase or download and will no longer be supported. Make the most of your initial Cisco VPN gateway investment, and take remote access to the next level.



 The highlights in brief:
The highlights in brief: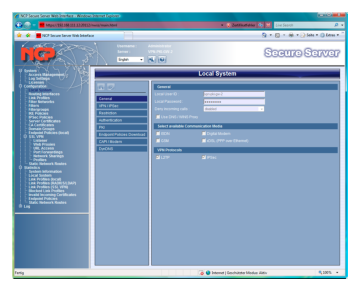 The highlights in brief:
The highlights in brief: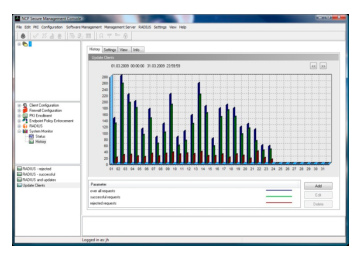 The highlights in brief:
The highlights in brief: